IDOR on the Shelf
Overview
Room URL: https://tryhackme.com/room/idor-aoc2025-zl6MywQid9
Difficulty: Medium
Category: IDOR
Date Completed: 12/5/2025
Objectives
- Understand the concept of authentication and authorization
- Learn how to spot potential opportunities for Insecure Direct Object References (IDORs)
- Exploit IDOR to perform horizontal privilege escalation
- Learn how to turn IDOR into SDOR (Secure Direct Object Reference)
Table of Contents
Introduction
Walk Through
Lessons Learned
Resources
Introduction
McSkidy's investigation into the elven gift distribution system has uncovered a critical security flaw that could compromise the entire operation. The application managing parent accounts and child records is vulnerable to Insecure Direct Object Reference (IDOR) attacks, allowing attackers to bypass authorization checks and access data belonging to other users without permission. This vulnerability demonstrates a fundamental breakdown in access control—the system authenticates users but fails to verify whether they have permission to view specific data. Through a series of escalating challenges, you'll learn how IDOR vulnerabilities manifest in different forms: from obvious sequential IDs to encoded values and cryptographic hashes. More alarmingly, you'll discover how even seemingly random identifiers like UUIDs can be predictable when generated using deterministic algorithms. Understanding these attack vectors is essential for securing applications against unauthorized data disclosure and horizontal privilege escalation.
Key Information
- Vulnerability Type: Insecure Direct Object Reference (IDOR) / Authorization Bypass
- Impact: Horizontal privilege escalation allowing access to other users' sensitive data
- Root Cause: Missing server-side authorization checks on data access requests
- Obfuscation Methods Encountered: Sequential IDs, Base64 encoding, MD5 hashing, UUID v1 generation
- Critical Lesson: Security through obscurity (encoding/hashing) is insufficient; server-side authorization verification is mandatory
Walk Through
- What does IDOR stand for?
Insecure Direct Object Reference
- What type of privilege escalation are most IDOR cases?
horizontal
- Exploiting the IDOR found in the
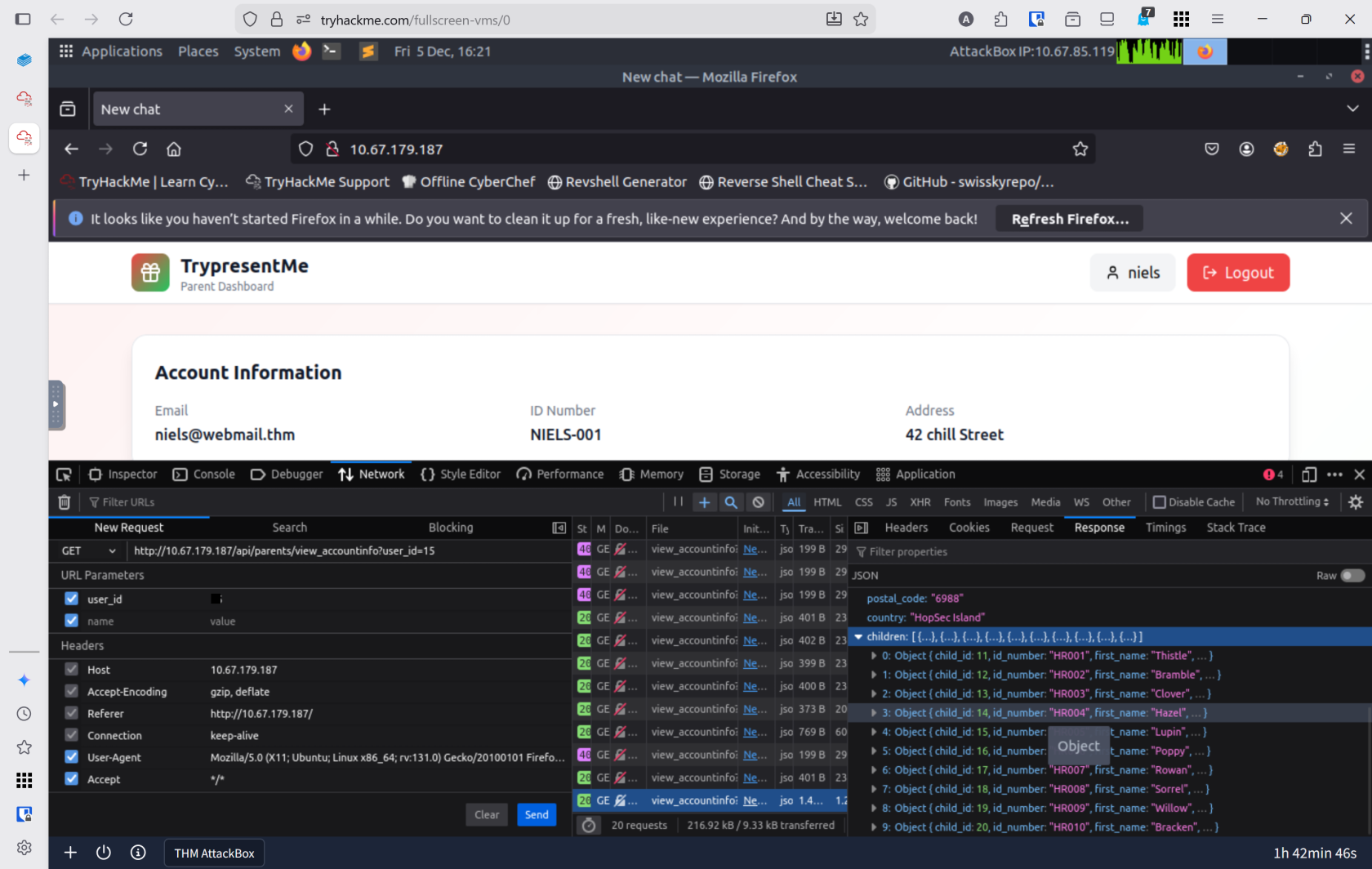
view_accountsparameter, what is theuser_idof the parent that has 10 children?- Spin up attack box and the target machine.
- Open the website at
http://10.67.179.187 - Log in using
niels:TryHackMe#2025 - Open developer tools
ctrl+shift+i - Open the network tab
- Click reload to load the network packets
- Click the one that says
view_accountinfo - On the right click responses
- Right click the packet on the left and select edit and resend
- Edit the
user_idand send
- Bonus Task: If you want to dive even deeper, use either the base64 or md5 child endpoint and try to find the id_number of the child born on 2019-04-17? To make the iteration faster, consider using something like Burp's Intruder.
- Used Burp Suite for this
- Open BurpSuite and turn intercept off
- Enable proxy in firefox and naviagte to the url
- View HTTP histroy in Burp Suite Proxy
- Send
/api/child/b64/Mg==to the intruder - Set
MG==as Payload - Set payload type to numbers
- I chose numbers
0-100 - Under payload processessing add encode to base64
- Start attack
- Click on the first packet
- At the bottom click view response
- Using the down arrow key I went through each until I found the entry I was looking for.
19
- Want to go even further? Using the /parents/vouchers/claim endpoint, find the voucher that is valid on 20 November 2025. Insider information tells you that the voucher was generated exactly on the minute somewhere between 20:00 - 24:00 UTC that day. What is the voucher code?
- The vouchers use UUID version 1 which is insecure, however, at this time, I am doing more research as I was unable to complete this one.
Lessons Learned
-
Mastered multiple IDOR exploitation techniques including direct ID manipulation, Base64-encoded parameter iteration using Burp Suite Intruder, and hash-based access control bypasses, demonstrating that obfuscation alone cannot prevent unauthorized access without proper server-side authorization checks
-
Understood the distinction between authentication and authorization and recognized that IDOR represents a horizontal privilege escalation vulnerability where authenticated users gain access to data they shouldn't be permitted to view, reinforcing that authorization must be verified on every request regardless of how object references are disguised