Detecting C2 with RITA
Overview
Room URL: https://tryhackme.com/room/detecting-c2-with-rita-aoc2025-m9n2b5v8c1
Difficulty: Medium
Category: C2
Date Completed: 12/22/2025
Objectives
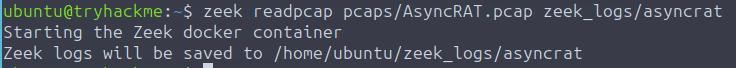
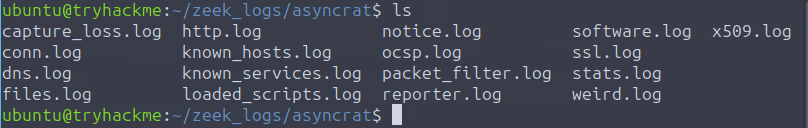
- Convert a PCAP to Zeek logs
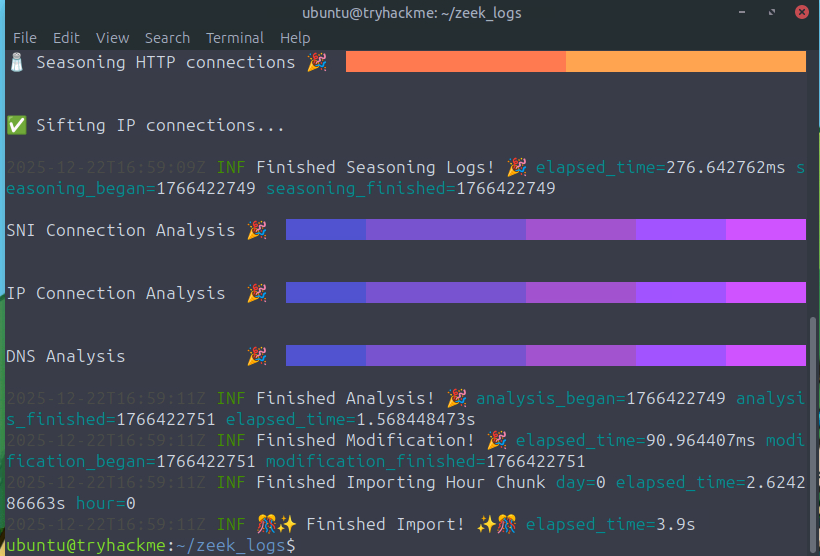
- Use RITA to analyze Zeek logs
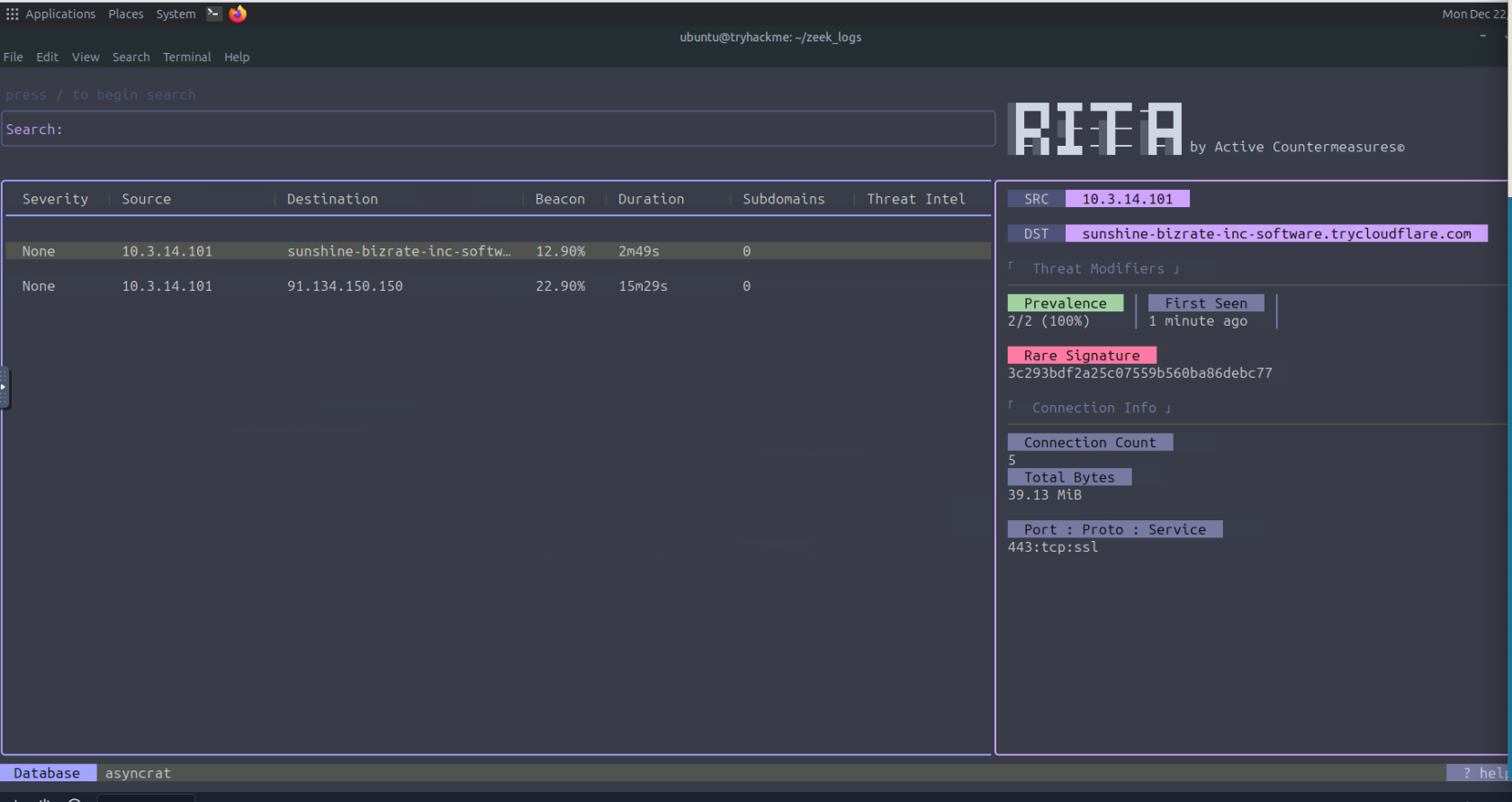
- Analyze the output of RITA
Table of Contents
Introduction
Walk Through
Lessons Learned
Resources
Introduction
This medium-difficulty challenge from TryHackMe's "Detecting C2 with RITA" room focuses on network traffic analysis and Command and Control (C2) detection. The challenge introduces Real Intelligence Threat Analytics (RITA), an open-source framework designed to identify C2 communication patterns through behavioral analysis of network logs. Participants are tasked with converting packet captures into Zeek logs, importing them into RITA, and leveraging RITA's analytics to identify malicious beaconing activity, suspicious connection patterns, and potential data exfiltration indicators.
The scenario involves analyzing network traffic captures from real-world malware incidents to detect AsyncRAT C2 infrastructure and other malicious communications hidden within legitimate-looking traffic. The challenge emphasizes the importance of understanding network-based indicators of compromise beyond signature-based detection.
Key Information
Features of RITA
- C2 beacon detection
- DNS tunneling detection
- Long connection detection
- Data exfiltration detection
- Checking threat intel feeds
- Score connections by severity
- Show the number of hosts communicating with a specific external IP
- Shows the datetime when the external host was first seen on the network
Behind RITA
- Only accepts data as Zeek logs
- Periodic connection intervals
- Excessive number of DNS queries
- Long FQDN
- Random subdomains
- Volume of data over time over HTTPS, DNS, or non-standard ports
- Self-signed or short-lived certificates
- Known malicious IPs by cross-referencing with public threat intel feeds or blocklist
Threat Modifiers:
- MIME type/URI mismatch: Flags connections where the MIME type reported in the HTTP header doesn't match the URI. This can indicate an attacker is trying to trick the browser or a security tool.
- Rare signature: Points to unusual patterns that attackers might overlook, such as a unique user agent string that is not seen in any other connections on the network.
- Prevalence: Analyzes the number of internal hosts communicating with a specific external host. A low percentage of internal hosts communicating with an external one can be suspicious.
- First Seen: Checks the date an external host was first observed on the network. A new host on the network is more likely to be a potential threat.
- Missing host header: Identifies HTTP connections that are missing the host header, which is often an oversight by attackers or a sign of a misconfigured system.
- Large amount of outgoing data: Flags connections that send a very large amount of data out from the network.
- No direct connections: Flags connections that don't have any direct connections, which can be a sign of a more complex or hidden command and control communication.
Query Types
- Severity: A score calculated based on the results of threat modifiers (discussed below)
- Source and destination IP/FQDN
- Beacon likelihood
- Duration of the connection: Long connections can be indicators of compromise. Most application layer protocols are stateless and close the connection quickly after exchanging data (exceptions are SSH, RDP, and VNC).
- Subdomains: Connections to subdomains with the same domain name. If there are many subdomains, it could indicate the use of a C2 beacon or other techniques for data exfiltration.
- Threat intel: lists any matches on threat intel feeds
Walk Through
- Start target machine
- How to use RITA
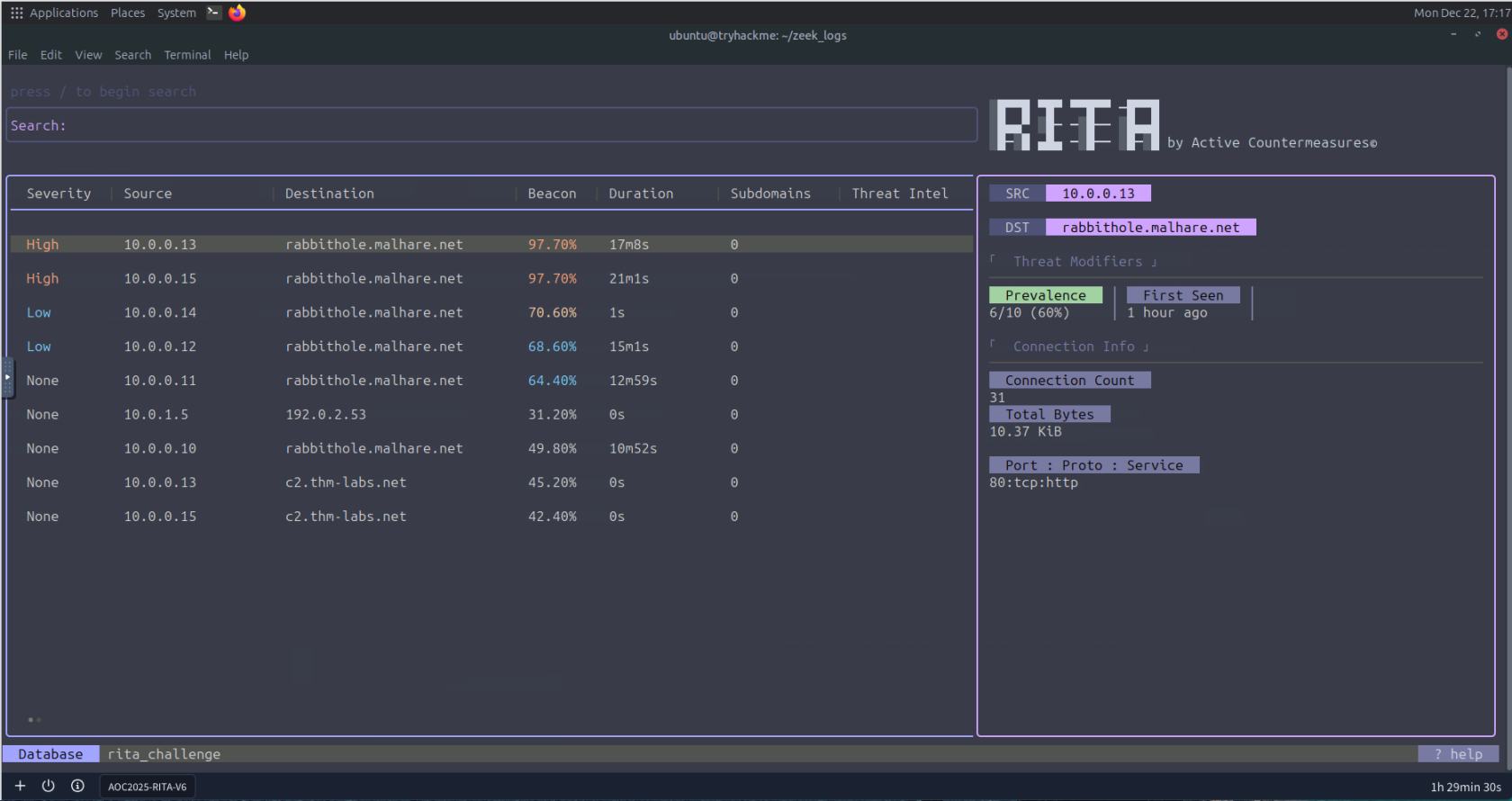
- How many hosts are communicating with malhare.net?
- Which Threat Modifier tells us the number of hosts communicating to a certain destination?
- Prevalence
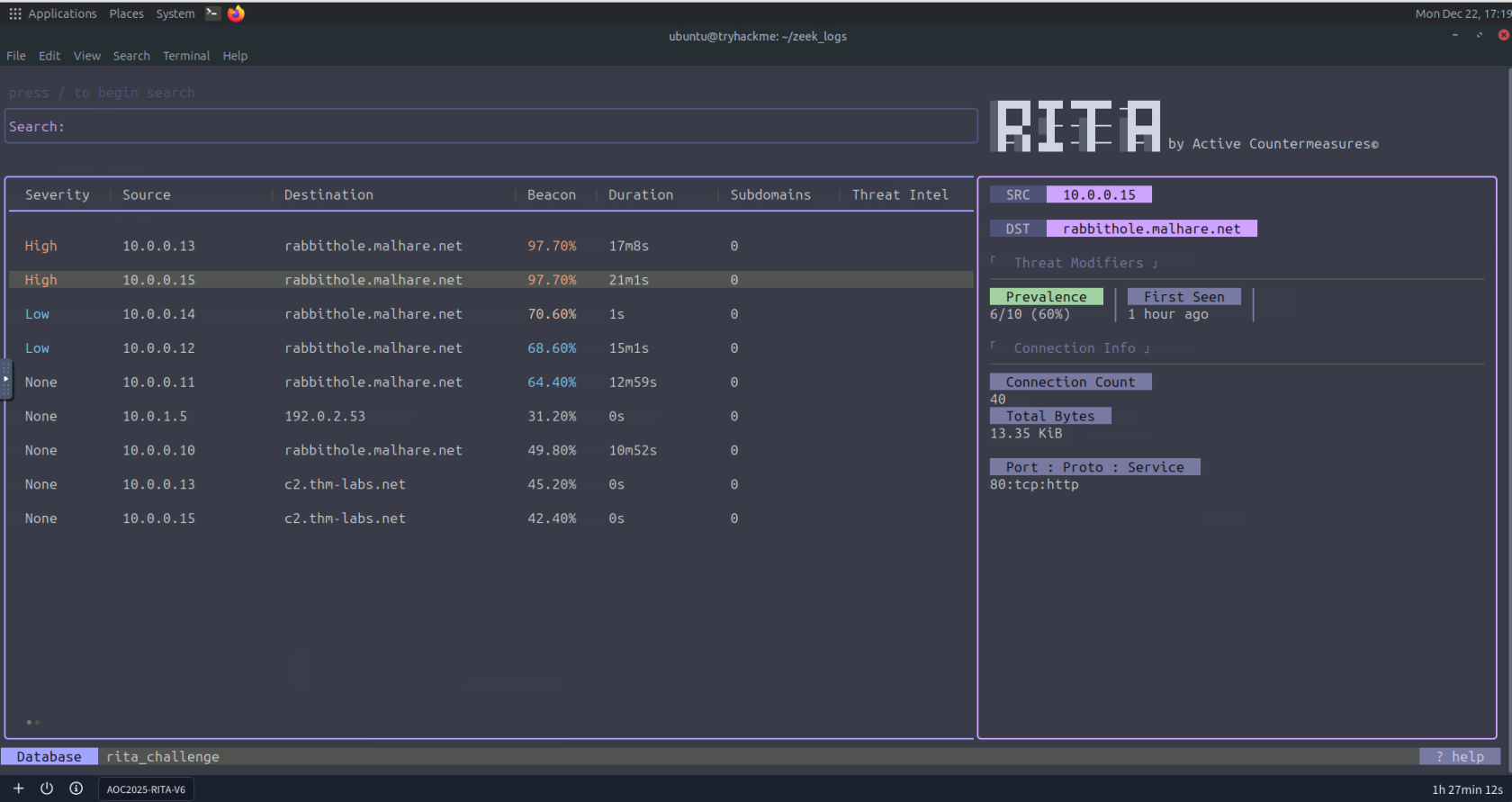
- What is the highest number of connections to rabbithole.malhare.net?
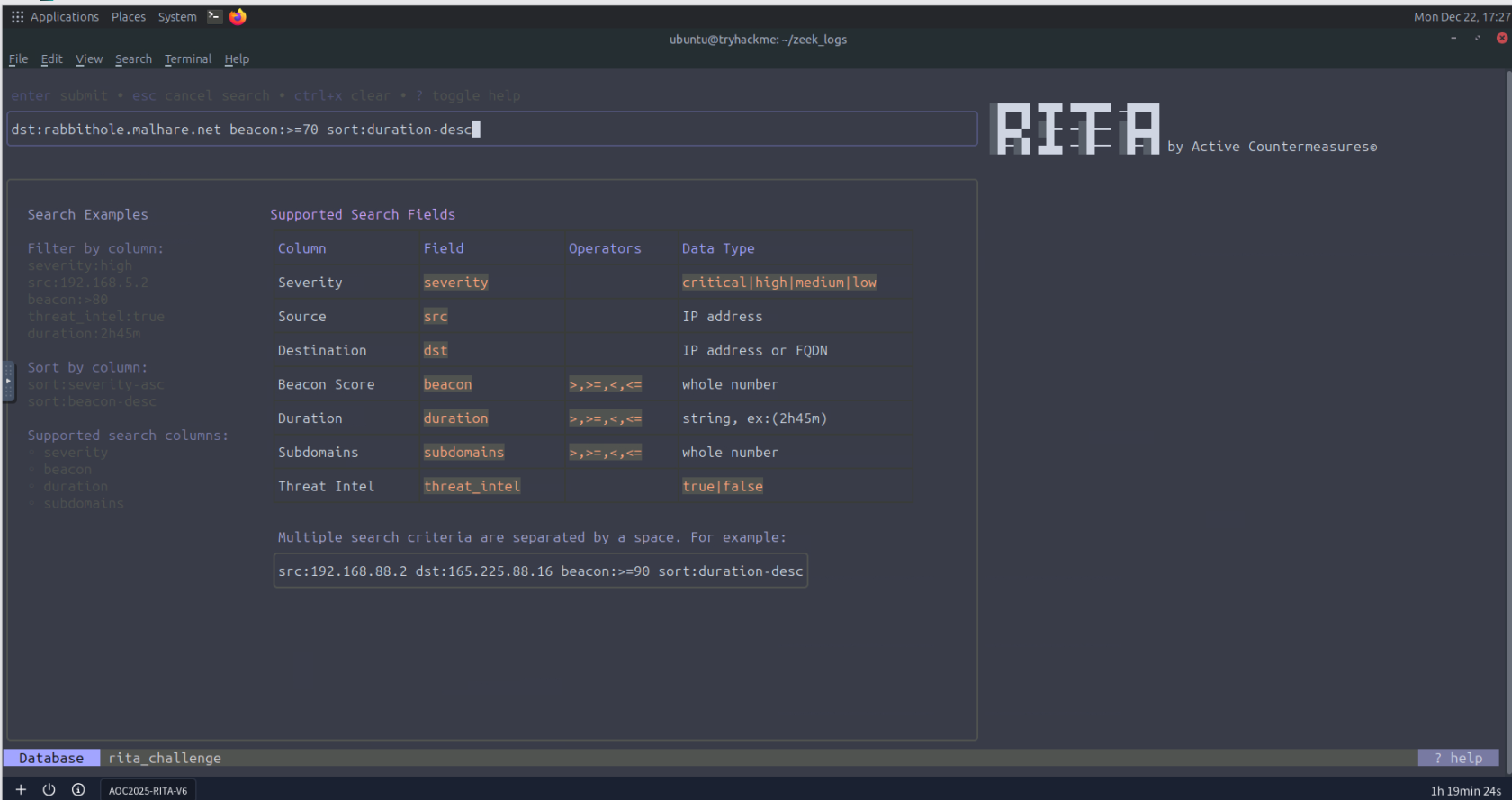
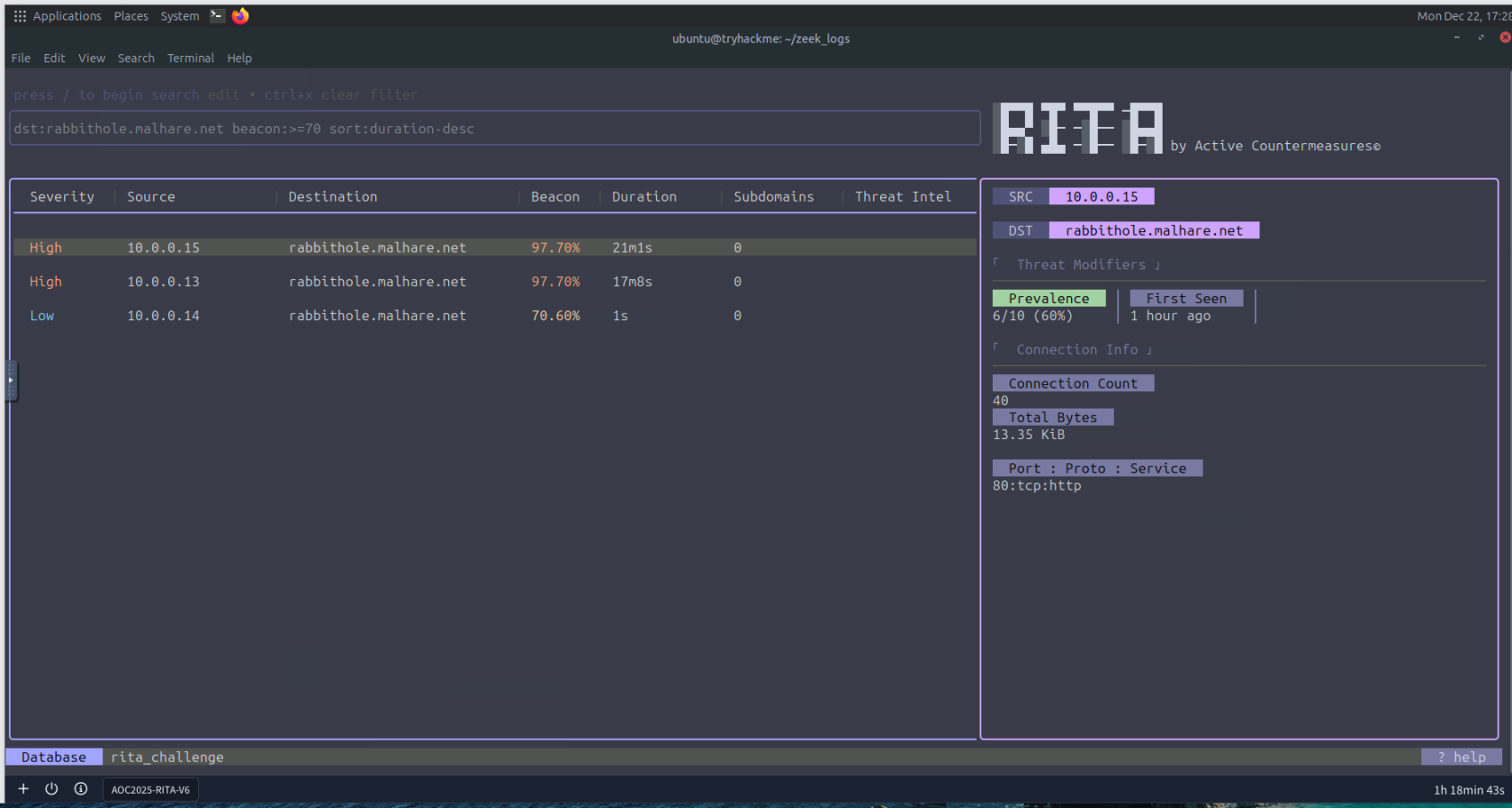
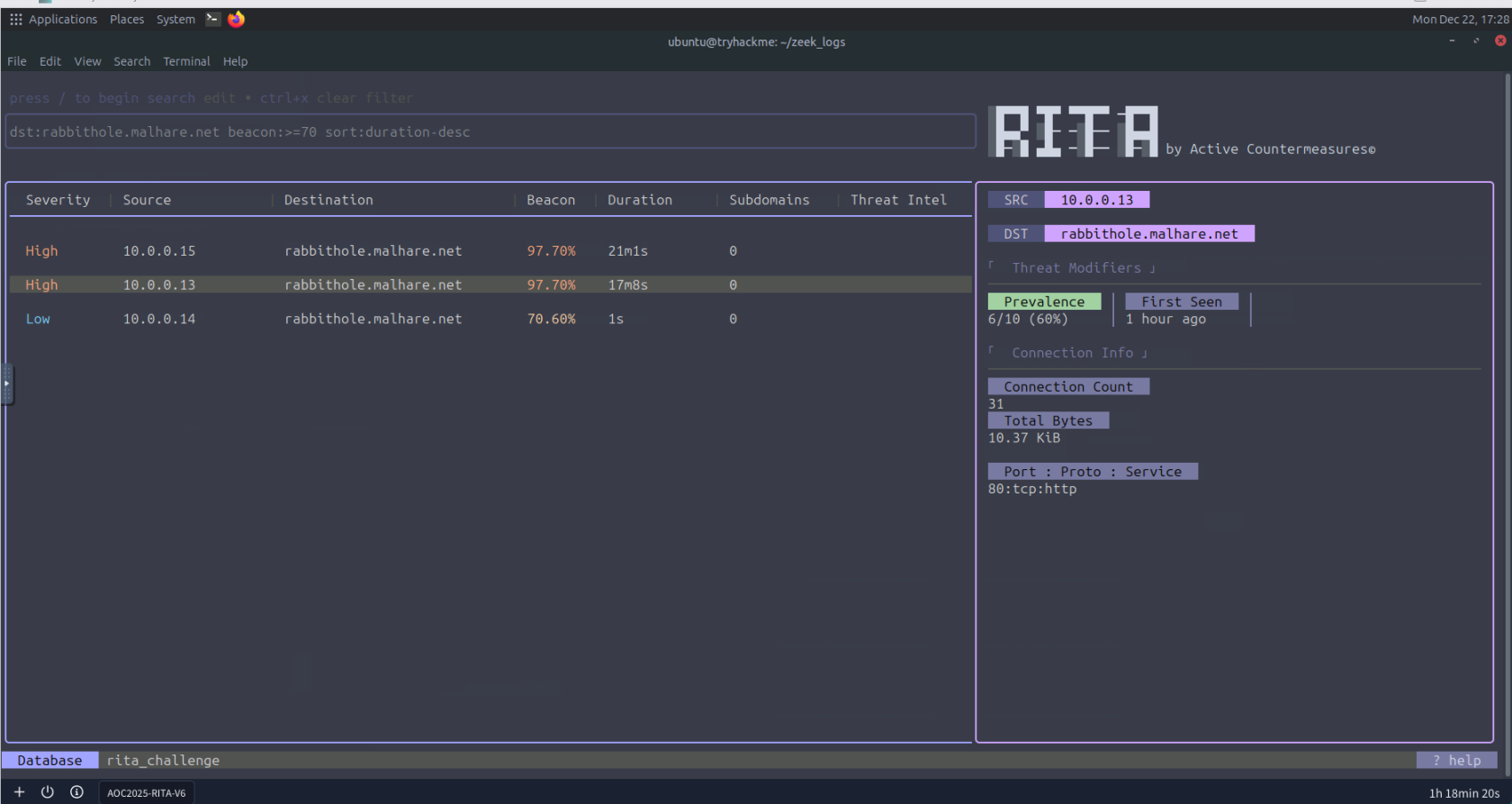
- Which search filter would you use to search for all entries that communicate to rabbithole.malhare.net with a beacon score greater than 70% and sorted by connection duration (descending)?
- Which port did the host 10.0.0.13 use to connect to rabbithole.malhare.net?
Lessons Learned
- Behavioral analysis trumps signature-based detection: RITA identifies C2 activity by correlating connection patterns, durations, and frequencies rather than relying on known malicious signatures. This approach catches novel threats and infrastructure rotation that evades traditional IOC-based detection.
- Zeek log enrichment provides crucial context: Converting PCAPs to structured Zeek logs enables sophisticated correlation across multiple protocol layers. The enriched metadata (SSL certificates, DNS queries, HTTP headers) reveals anomalies invisible in raw packet captures.
- Prevalence is a powerful indicator: When only a small subset of internal hosts communicate with an external destination, it warrants immediate investigation. Legitimate services typically show broad adoption patterns across the network.
- Long connection durations violate normal application behavior: Most HTTP/HTTPS connections are stateless and short-lived. Persistent connections lasting minutes or hours strongly indicate C2 channels, especially when combined with periodic beaconing.