Phishing Exercise for TBFC
Overview
Room URL: https://tryhackme.com/room/phishing-aoc2025-h2tkye9fzU
Difficulty: Easy
Category: Phishing
Date Completed: 12/2/2025
Objectives
SetUnderstandupwhatandsocialexecuteengineeringais- Learn
harvestingthe types of phishing - Explore
byhowhostingredateams create fakeTBFC portalloginpagepages - Use the Social-Engineer Toolkit
(SET)totargetsendfactory staff. Capture harvested credentials by monitoring the fake login portal to intercept username and password entries submitted by the target user.Identify the TBFC portal password by analyzing the credentials obtained from thea phishingattack.Verify credential reuse by testing whether the harvested admin credentials are also used on theemailportal (http://MACHINE_IP).Extract sensitive operational information by accessing the factory user's mailbox to determine the total number of toys expected for delivery, demonstrating the impact of a successful credential compromise on TBFC's operations.
Table of Contents
Introduction
Walk Through
Lessons Learned
Resources
Introduction
TBFC's defenses are tested once more, this time through a sophisticated social engineering campaign. The red team orchestrates a phishing attack targeting factory staff, crafting a convincing email from a trusted shipping partner and backing it with a fake login portal designed to harvest credentials. This challenge demonstrates how social engineering exploits human psychology—leveraging urgency, authority, and trust—to bypass even well-intentioned security awareness training. The attack succeeds in capturing working credentials, revealing a critical vulnerability: no matter how robust technical defenses are, they can be undermined if employees fall victim to carefully crafted phishing schemes. Understanding both the attacker's methodology and the psychological triggers that make phishing effective is essential for building a human-centric defense strategy.
Key Concepts
S.T.O.P
- Suspicious?
- Telling me to click something?
- Offering me an amazing deal?
- Pushing me to do something now?
S.T.O.P (2)
- Slow down. Scammers run on your adrenaline.
- Type the address yourself. Don’t use the message’s link.
- Open nothing unexpected. Verify first.
- Prove the sender. Check the real From address/number, not just the display name.
Walk Through
- Launch the target machine and the attack box.
- What is the password used to access the TBFC portal?
- There is a script located at
~/Rooms/AoC2025/Day02to sping up the server to start listening for credentials. - Opened terminal and went to the directory
cd ~/Rooms/AoC2025/Day02 - Launched the script using
./server.py - Confirmed the webpage is up and running at
http://localhost:8000 - Using the Social-Engineering-Toolkit (SET) to deliver the link to the victim to collect credentials.
setoolkitto launch the toolkit in terminal- Option
1for social engineering attacks - Option
5for mass mailer - Option
1for send to single email - Send To:
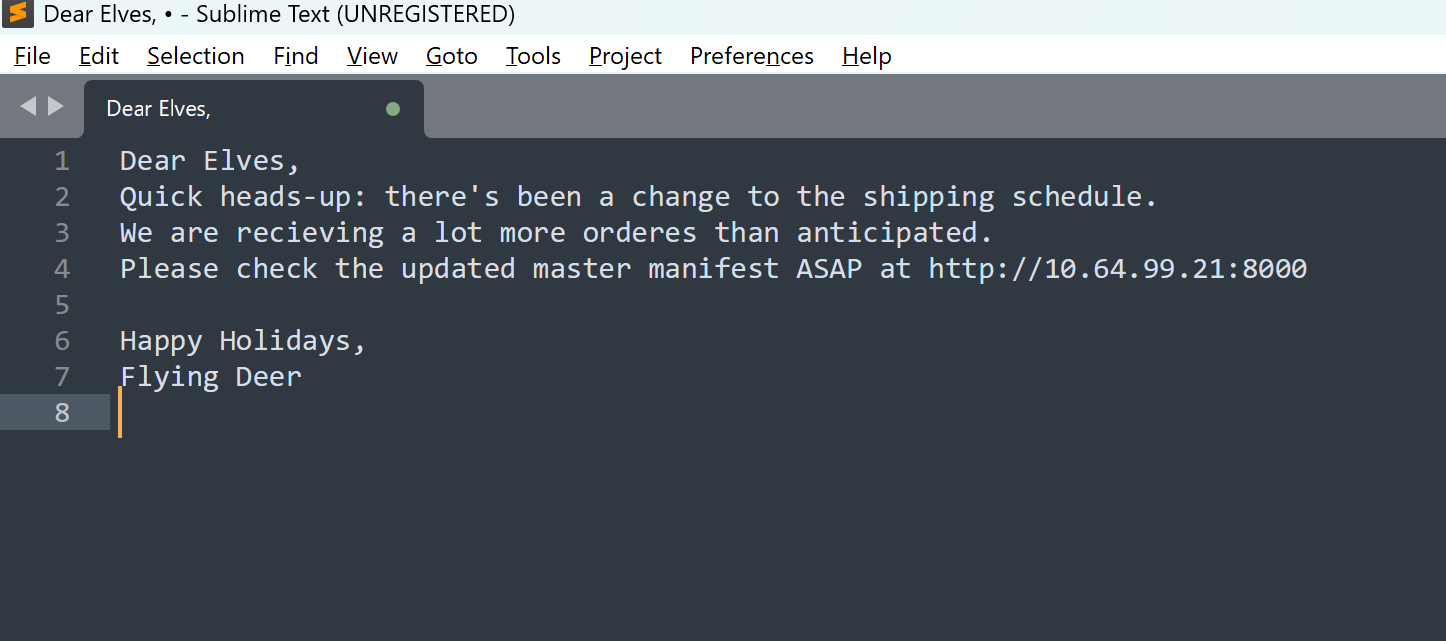
[email protected] - Option
2use your own server or open relay - From Address:
[email protected] - From Name:
Flying Deer - Username for open relay
- Password for open relay
- SMTP Email Server Address
10.64.130.91(target ip address) - Port Number
25 - Flag as High Priority
no - Attach a file
n - Attach an inline file
n - Email Subject
Shipping Schedule Changes(should be something convincing) - Send email as
htmlorplaintext - The body of the email line by line. Use
ENDto indicate end of email. - Email Has been sent
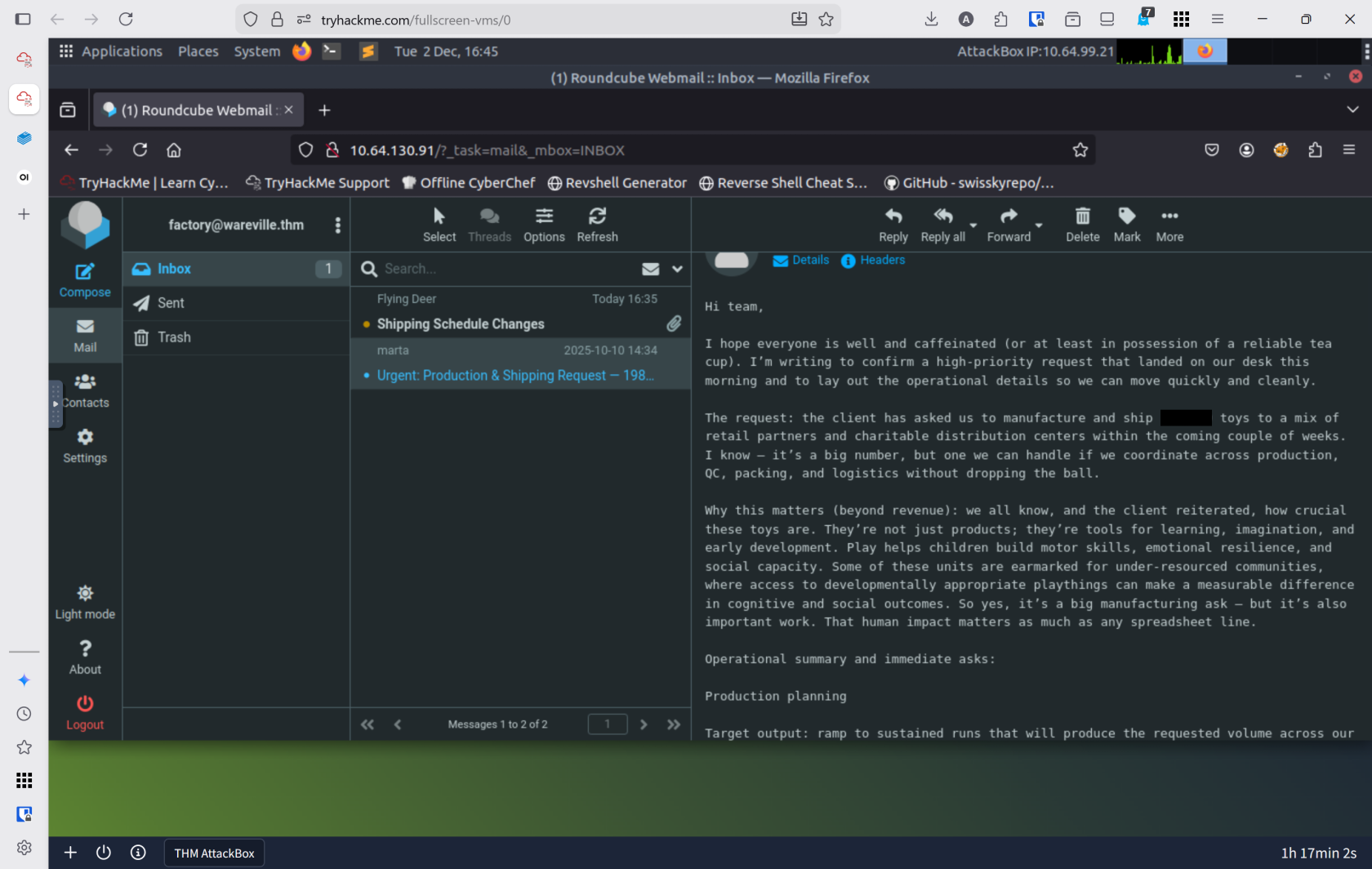
- Switch back to terminal with
server.pyrunning to see if it captured credentials - Username:
adminPassword:u***********m 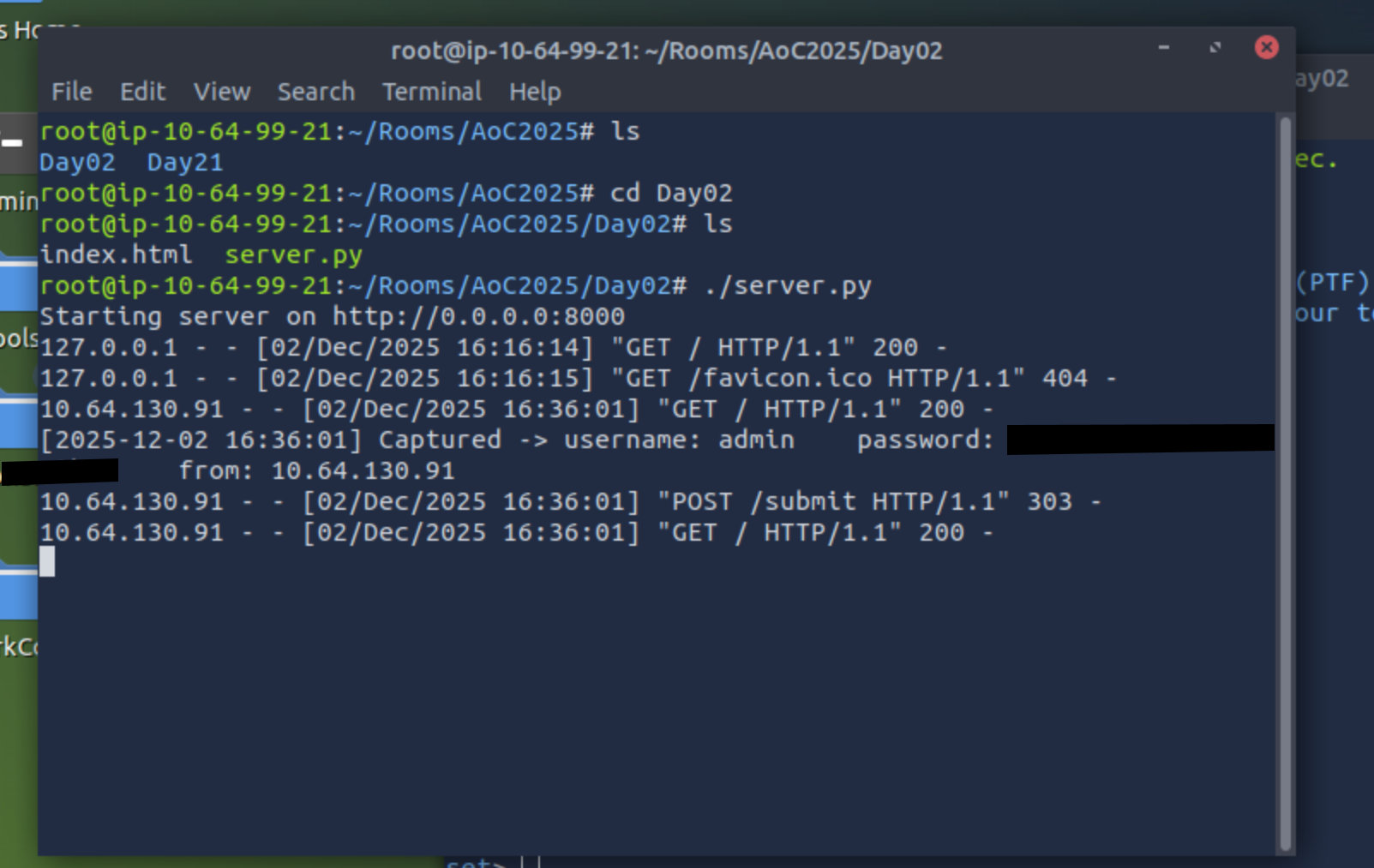
- There is a script located at
- Browse to
http://10.64.130.91from within the AttackBox and try to access the mailbox of thefactoryuser to see if the previously harvestedadminpassword has been reused on the email portal. What is the total number of toys expected for delivery?